Hackers' Latest Trick: How a 4G-Enabled Raspberry Pi Breached a Bank's Network
Hackers' Latest Trick: How a 4G-Enabled Raspberry Pi Breached a Bank's Network
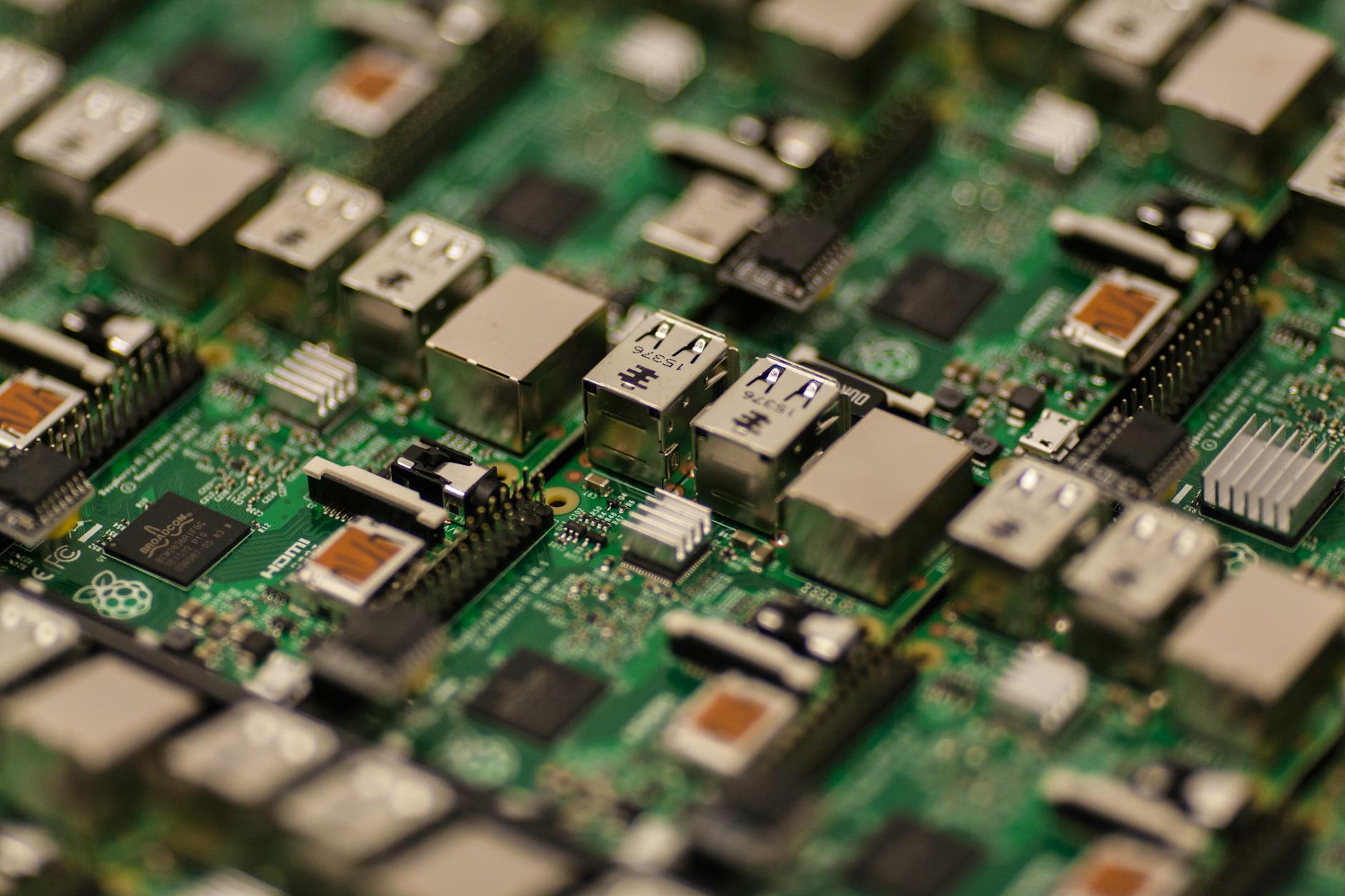
A recent cyber attack on a bank's network has raised the stakes in the cat-and-mouse game between hackers and cybersecurity experts. In a daring heist, cybercriminals used a 4G-enabled Raspberry Pi device to gain unauthorized access to the bank's system, highlighting the vulnerabilities of modern banking systems and the need for robust security measures to prevent such attacks.
The Anatomy of the Attack
Driven by the promise of riches, the hackers exploited a weakness in the bank's network to gain access. Once inside, they deployed a 4G-enabled Raspberry Pi, a tiny, low-cost computer that can be easily concealed and connected to the internet via cellular networks. This allowed them to remotely access and control the device, using it to manipulate the bank's systems and steal sensitive data.
Why Raspberry Pi?
The use of a Raspberry Pi in this attack is significant, as it highlights the growing popularity of IoT devices as tools for cybercrime. "The increasing use of IoT devices in cyber attacks is a trend that's here to stay," says Dr. Maria Rodriguez, a leading expert in cybersecurity. "These devices are small, inexpensive, and easily accessible, making them an attractive option for hackers."
The Implications of This Attack
This incident has far-reaching implications for the banking industry and beyond. It demonstrates that even seemingly secure systems can be compromised, and that hackers are constantly adapting and innovating to stay one step ahead of security measures. The use of IoT devices as attack vectors raises concerns about the vulnerabilities of connected systems and the need for robust security protocols to prevent similar attacks.
Lessons Learned: Enhancing Security Measures
This incident serves as a wake-up call for the banking industry and other organizations to re-evaluate their security measures. To prevent similar attacks, it is crucial to:
- Implement robust network segmentation to limit lateral movement in case of a breach (Learn more about network segmentation)
- Enhance monitoring and detection capabilities to identify and respond to suspicious activity
- Conduct regular security audits and penetration testing to identify vulnerabilities
- Implement multi-factor authentication and access controls to prevent unauthorized access
- Educate employees on the risks and consequences of cyber attacks and the importance of cybersecurity best practices (Read more: Our Guide to Employee Cybersecurity)
The Future of Cyber Attacks: What's Next?
This incident marks a new era in cyber attacks, where hackers are leveraging innovative technologies to exploit vulnerabilities. As IoT devices become increasingly ubiquitous, it is essential for organizations to stay vigilant and proactive in their security measures. "The future of cyber attacks will be characterized by more sophisticated and targeted attacks," says Dr. Rodriguez. "Businesses need to invest in robust security protocols and stay ahead of the evolving threat landscape."
Key Takeaways
Here are the key takeaways from this incident:
- The use of IoT devices in cyber attacks is a growing trend
- Robust security measures, including network segmentation and monitoring, are crucial to preventing similar attacks
- Organizations need to stay vigilant and proactive in their security measures to stay ahead of the evolving threat landscape
Conclusion
In conclusion, the failed ATM heist that involved a 4G-enabled Raspberry Pi highlights the ever-present threat of cyber attacks and the need for organizations to prioritize security. By understanding the anatomy of the attack, the implications, and the lessons learned, we can work together to build a more secure digital future.


Comments
Post a Comment